
HIPAA applies to any organization that creates, accesses, or processes protected health information (PHI).
Auditious helps covered entities and business associates meet HIPAA Security, Privacy, and Breach Notification requirements through AI-driven controls, automated evidence collection, and continuous monitoring—so you can protect PHI and build trust with confidence.
Start with HIPAA Administrative, Physical, and Technical Safeguards already mapped to your business, infrastructure, and risk profile.
Threatsafe uses AI to analyze your environment and align controls across all three HIPAA safeguard categories—reducing manual scoping, misalignment, and the risk of costly violations from day one.
Eliminate last-minute scrambling with automated, always-on evidence gathering across your cloud, identity, DevOps, and endpoint stack.
Threatsafe continuously collects, validates, and timestamps HIPAA-ready evidence so your compliance posture stays current—not stale—and you're always prepared for an OCR audit or breach inquiry.
Know exactly where you stand against HIPAA requirements at all times, across every system that touches Protected Health Information.
Our AI engine detects safeguard gaps, policy drift, and non-compliance signals in real time—prioritizing risks by severity and regulatory impact before HHS, OCR, or your customers find them.
Turn compliance findings into actionable fixes without needing a dedicated compliance team or outside consultant.
Threatsafe provides step-by-step remediation guidance mapped directly to HIPAA controls, assigns ownership, tracks progress, and generates audit-ready Risk Assessment reports—shortening your compliance cycle and reducing back-and-forth with regulators.




Everything you need to know about achieving and maintaining HIPAA compliance with Threatsafe.
HIPAA (Health Insurance Portability and Accountability Act) sets the standard for protecting sensitive patient health information. Any organization that handles Protected Health Information (PHI) — including healthcare providers, health plans, healthcare clearinghouses, and their business associates — must comply. This includes SaaS companies, cloud vendors, and tech platforms that process or store health data on behalf of covered entities.
A Covered Entity is a healthcare provider, health plan, or clearinghouse that directly handles PHI. A Business Associate is any third-party vendor — like a cloud provider, billing platform, or analytics tool — that creates, receives, maintains, or transmits PHI on behalf of a covered entity. Business Associates must sign a BAA (Business Associate Agreement) and are directly liable under HIPAA. Threatsafe helps both types achieve and maintain compliance.
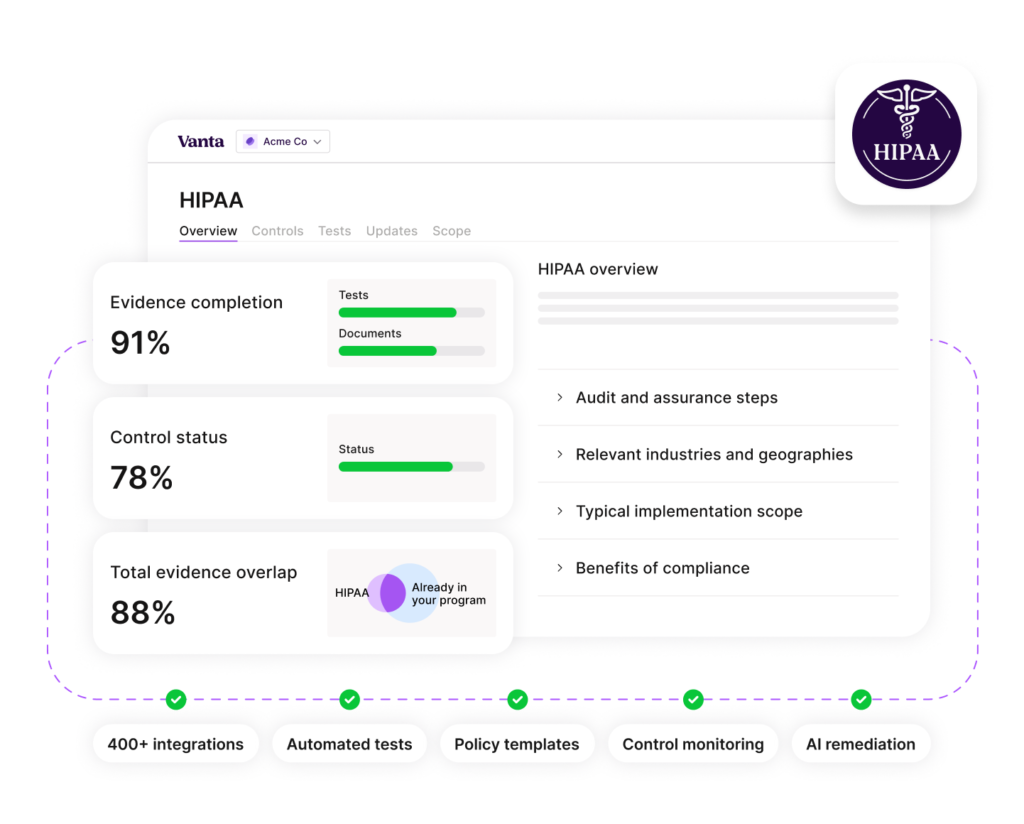
Threatsafe connects read-only to your cloud infrastructure, identity providers, and endpoint tools — like AWS, GCP, Azure, Okta, and GitHub. It automatically maps your existing controls to HIPAA's Administrative, Physical, and Technical Safeguards, collects timestamped evidence continuously, and flags gaps in real time. No more manual screenshots or spreadsheet tracking.
HIPAA's Security Rule requires three types of safeguards. Administrative Safeguards cover policies, workforce training, and risk management — Threatsafe provides pre-built policy templates and employee training workflows. Physical Safeguards govern access to facilities and hardware — Threatsafe monitors device compliance and access logs. Technical Safeguards protect electronic PHI through encryption, access controls, and audit controls — Threatsafe continuously validates these against your cloud environment.
Unlike SOC 2, HIPAA does not have an official government-issued certification. However, organizations must conduct and document annual risk assessments, maintain audit logs, and demonstrate compliance during HHS investigations or breach inquiries. Threatsafe generates audit-ready documentation and risk assessment reports that serve as proof of due diligence — protecting you in the event of an OCR audit or data breach investigation.
HIPAA penalties range from $100 to $50,000 per violation, with annual maximums up to $1.9 million per violation category. Willful neglect can result in criminal charges. Threatsafe continuously monitors your HIPAA controls, detects gaps before they become violations, and provides step-by-step remediation guidance — dramatically reducing your exposure and demonstrating good-faith compliance efforts to regulators.
Most organizations can reach a strong HIPAA compliance posture within 4 to 8 weeks using Threatsafe, depending on the complexity of your infrastructure and the number of gaps identified. Threatsafe's pre-mapped controls, automated evidence collection, and AI-guided remediation eliminate the manual work that typically makes HIPAA preparation slow and expensive.
Ready to become HIPAA compliant? Our experts will guide you every step of the way.
Talk to a HIPAA Expert →+2 237 467 134-98
example@email.com
Elgin St. Celina, Delaware - 102
Offers are valid for a limited time only and reflect multi-annual discounts. Other terms and conditions may apply. Click Here